|
AWS Topic: AWS Config Date:8/19/2021 |
||||||||||||||
|
What is the purpose of the service? AWS config is a service that enables
you to ASSESS, AUDIT, and EVALUATE the configurations for all of
your AWS resources. You can review changes in configurations,
relationships between AWS resources, and see detailed resource configuration
histories. |
||||||||||||||
|
Why does it exist? What problem does it solve? What business
purpose does it enable? It exists to simplify compliance auditing, security analysis, change
management, and operational troubleshooting. You can
determine your overall compliance against the configurations specified in
internal guidelines. With so many configuration options, it
can be a challenge to ensure your resources are efficient, security and complying
with best practices. This can help you
determine if your resources comply with government regulations or industry
best-practices across all regions. AWS
Config is a fully managed service that provides you with an AWS resource
inventory, configuration history, and configuration change notifications to enable security and
governance |
||||||||||||||
|
What are its features and benefits? · Continuous Monitoring – continuously monitor and record configuration changes of your AWS resources. · Continuous Assessment – continuously audit and assess overall compliance of AWS resources · Change Management – track relationships among resources and resource dependencies. · Operational Troubleshooting – get a comprehensive history of resource configuration changes to simplify troubleshooting. · Enterprise-wide compliance monitoring – multi-account, multi-region data aggregation · Support for third party resources – can be primary tool to perform configuration audit and compliance of AWS and third-party resources. (ie Git-hub, Microsoft AD resources, or an on-premises server into AWS) · With AWS config you avoid the complexity of installing and updating agents for data collection or maintaining large databases of configurations. |
||||||||||||||
|
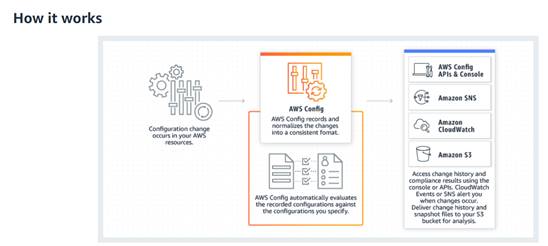
How does it work? AWS
Config records point-in-time configuration details for your AWS resources as Configuration Items (CIs) You define policies, and then receive
a notification when the resource deviates from these rules. If it finds a non-compliant resource, it provides
automatic remediation to get back to security and compliant status. ·
Record changes of your AWS resources ·
Inventory of AWS resources and configurations,
as well as software configurations. ·
Sends SNS notification for review and action. ·
Continuous Assessment ·
Define rules for provisioning and configuring
resources ·
Noncompliant configurations trigger an SNS
notification and cloudwatch events.
|
||||||||||||||
|
When should it be used? (Use cases) · DISCOVERY - When you need to discover resources that exist in your current account, record the configuration, and capture any changes to these configurations. Retains configuration details for deleted resources. · CONTINUOUS COMPLIANCE (Compliance as CODE) – use your AWS config rules to create code that is deployed as a “conformance package” using AWS Systems Manager. · TROUBLESHOOTING – identify recent configuration changes that may have caused problems in your configuration. · SECURITY ANALYSIS – continuously monitor AWS resources for security weaknesses
|
||||||||||||||
|
Who uses this type of service? – Auditors, Security Professionals,
Operations managers, who are concerned about the security, compliance, and
performance of applications. – System engineers who are troubleshooting
configuration issues. |
||||||||||||||
|
What is it NOT appropriate for? Where
is it NOT a fit? |
||||||||||||||
|
Are there services related to this AWS
feature? ·
You
can use it to track activity logs for Lambda, EC2, S3, for specific events. ·
SNS
is used for notification of non-compliance. ·
CloudTrail
records are used to correlate configuration changes to particular
events in your account. You can use a CI to answer
“What did my AWS resource look like?” at a point in time. You can use AWS
CloudTrail to answer “Who made an API call to modify this resource? ·
Author
remediation actions with AWS Systems Manager Automation documents to package
AWS config rues into a comformance pack that can be
deployed across and organization. ·
AWS Security Hub is a security and compliance
service that provides security and compliance posture management as a
service. It uses AWS Config and Config rules as its primary mechanism to
evaluate the configuration of AWS resources. AWS Config rules can also be
used to evaluate resource configuration directly. Config rules are also used
by other AWS services, such AWS Control Tower and AWS Firewall Manager |
||||||||||||||
|
What roles or permissions do I need to
use the service? AWS
account administrator |
||||||||||||||
|
What does it cost to use this service? You are charged based on: · The number of configuration items recorded · The number of active AWS Config Rule evaluations · The number of conformance pack evaluations in your account
|
||||||||||||||
|
Where do I access the service? You
can lookup current and historical resource configuration using the AWS
Management Console, AWS Command Line Interface or SDKs |
||||||||||||||
|
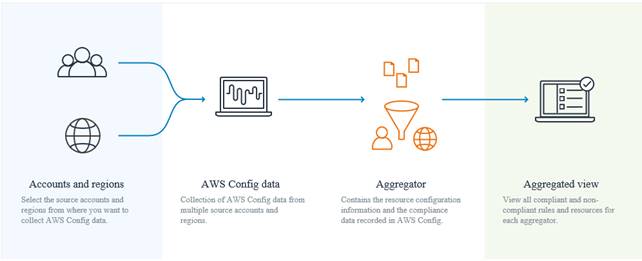
What are the service features? Availability: Multi AZ, Multi-Region? Which regions do not have this service? ·
Data aggregation in AWS Config allows you to
aggregate AWS Config data from multiple accounts and regions into a single
account and a single region. Multi-account data aggregation is useful for
central IT administrators to monitor compliance for multiple AWS accounts in
the enterprise.
Fault-Tolerance/Resilience? 1.
Automatic Remediation of Non-compliant
resources 2.
Evaluate
existing configuration against desired ones and continuously track changes
against your other resources to better analyze efficiency or performance 3.
Dashboard
displays on your configuration console so you can see compliance and a
resource inventory at a glance. 4.
Integrate
AWS with other AWS services |
||||||||||||||
|
How do I create the service? What information is required to create the
service? What are the requirements for
the service? Definitions… 1.
A configuration item
is a record of the
configuration state of a resource in your AWS account 2.
Config Rule represents desired
configurations for a resource and is evaluated against configuration
changes on the relevant resources, as recorded by AWS Config. AWS
managed rules: AWS managed rules are pre-built and managed by AWS. You simply
choose the rule you want to enable, then supply a few configuration
parameters to get started. Customer managed rules: Customer managed
rules are custom rules, defined and built by you. You can create a function
in AWS Lambda that can be invoked as part of a custom rule and these
functions execute in your account. You can create up to 150 rules in
your AWS account by default 3.
Any rule can be setup as a change-triggered rule or as a
periodic rule. A change-triggered rule is executed when AWS Config records a
configuration change for any of the resources specified. Additionally, one of
the following must be specified: ·
Tag Key:(optional
Value): A tag key:value
implies any configuration changes recorded for resources with the specified
tag key:value will trigger an evaluation of the
rule. ·
Resource type(s): Any configuration changes recorded for any
resource within the specified resource type(s) will trigger an evaluation the
rule. ·
Resource ID: Any changes recorded to the resource specified by
the resource type and resource ID will trigger an evaluation of the rule. 4.
Evaluation of a rule determines whether a
rule is compliant with a resource at a particular point in time. Config
rules will capture and store the result of each evaluation. This result will
include the resource, rule, time of evaluation and a link to Configuration
Item (CI) that caused non-compliance. A resource is compliant if
complies with all rules that apply to it. Otherwise it is noncompliant 5.
A conformance pack is a collection of
Config rules and remediation actions that is built using a common framework and
packaging model in AWS Config 6.
An aggregator is an AWS Config resource type
that collects AWS Config data from multiple accounts and regions. Use an
aggregator to view the resource configuration and compliance data recorded in
AWS Config for multiple accounts and regions. 7.
Components of a configuration item: https://docs.aws.amazon.com/config/latest/developerguide/config-item-table.html 8.
|
||||||||||||||
|
Notes and questions: 1.
Can
this audit non-cloud resources? – Apparently yes – it says you can publish
the configuration of third-party servers on-premise. 2.
|